11-19, 18:30–22:30 (Canada/Eastern), Hackfest - Track 1
Language: English
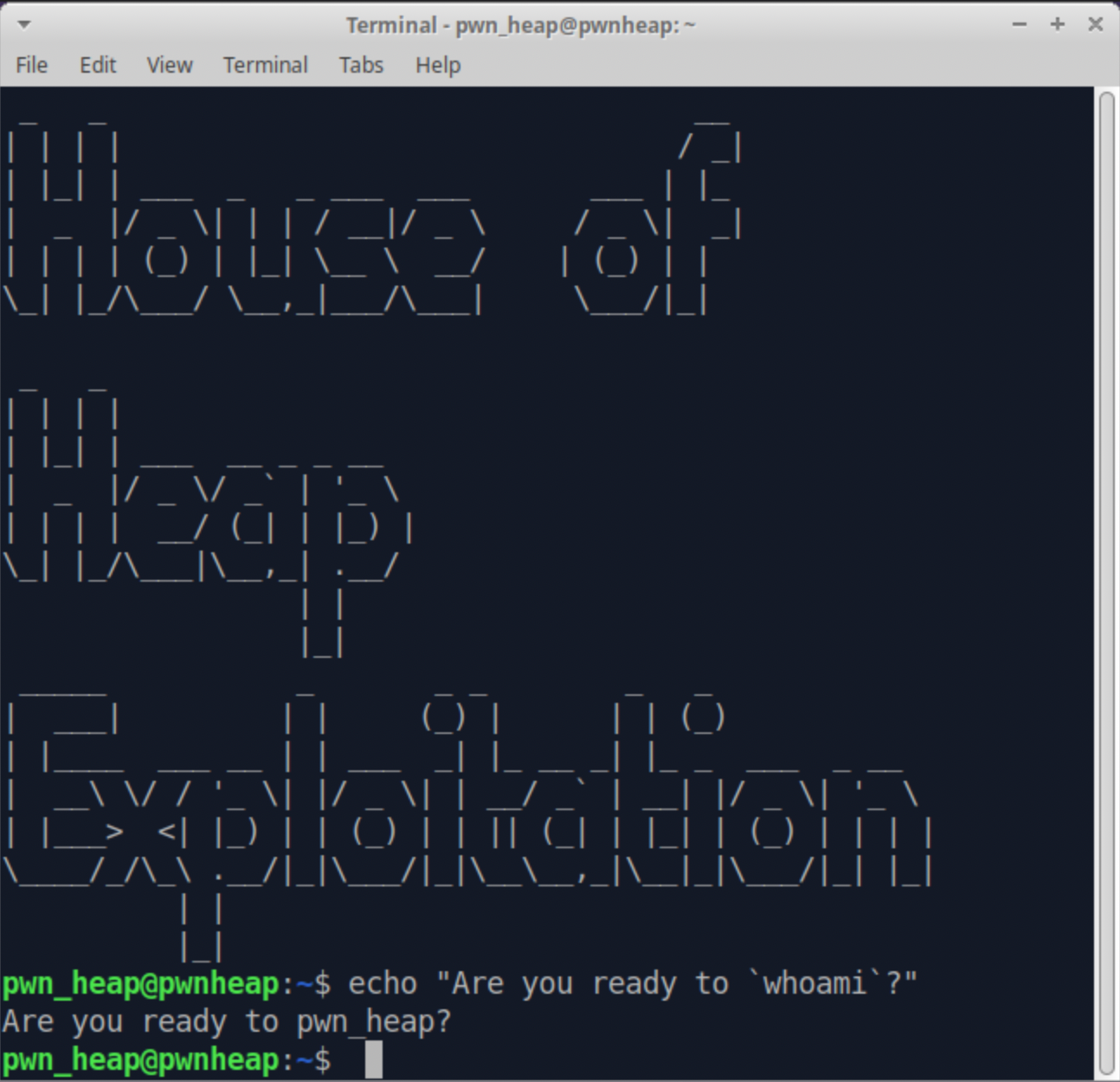
Heap exploitation is an incredibly powerful tool for a hacker. As exploit mitigations have made exploitation more difficult, modern exploit development has moved to the heap. However, heap exploitation is a subject that has evaded many people for years for one reason: they focus on the techniques instead of the allocator. By learning with an allocator first style, the techniques are easily understood and practical to use.
This workshop is for learning heap exploit development in GLibC Malloc, which is the deallocate allocator on most Linux distros. With this hands-on introduction into GLibC Malloc heap exploitation you will learn how the allocator functions, heap specific vulnerability classes and how to pwn with a variety of techniques. Whether you're an avid CTFer, trying to beat a pwnables challenge or exploiting 0-days, this course is good for adding another tool to the tools arsenal. After taking this course you will understand the GLibC Malloc allocator, be able to discover heap specific vulnerability classes and pwn the heap with a variety of techniques, with the capability to easily learn more.
The workshop starts with an introduction to how the allocator works then dives into heap specific vulnerability classes. Once the ground-work is set, 3 different techniques specific to the allocator are analyzed, which are only possible after going through the previous two sections. Understanding how the allocator works is crucial to pwning the heap!
If you plan on taking the workshop, please do two things:
- Install the virtual machine (VM) prior to the workshop. It is about 3.5 Gb and the link is below with installation steps: https://drive.google.com/drive/folders/1MmMP-oVf7hZYnRwLV06KKXn_K9__NQfV?usp=sharing
- Join the slack channel! We will be placing content and answering questions in here: https://join.slack.com/t/heapworkshoph-4um8827/shared_invite/zt-yjqhuvxf-3eBDGhW0px4c_7PUS2pwow
The outline for the workshop is below:
- Module 1 - Introduction to the GLibC Heap Allocator:
- Basic Data structures
- Chunks
- Bins (Free Chunks Handling)
- Challenge #1: Fixing a chunk
- Arenas
- Malloc & Free Ordering
- Challenge #2: Heap feng shui (if time permits)
- Module 2 - Heap Vulnerability Classes:
- Ideal heap environment testing setup
- Heap buffer overflows
- Use after frees
- Double frees
- Challenge #3: Use after free
- Module 3 - Fd Poisoning:
- Understanding the TCache Bin
- Exploiting fd pointers
- Fastbin Variation
- Challenge #4: Fd Poison
- Module 4: Unlink:
- Understanding the original bins (unsorted, small and large)
- Removing a chunk from a bin
- Unlink attack for arbitrary write primitive
- Unsafe unlink attack
- Challenge #5: Unlink Attack
- Module 5 - Overlapping Chunks:
- Understanding the size and prev_size chunk metadata
- Corrupting the size field
- Overlap chunks by growing and shrinking
- Other variations
- Challenge #6: Overlap two chunks
- Conclusion
Maxwell Dulin (Strikeout) is a security consultant at Security Innovation hacking all things under the sun, from robots to web applications. Maxwell has published many articles for a plethora of heap exploitation techniques, assorted web application hacking exploits, machine learning and IoT device vulnerability hunting. Previously spoken at DEF CON 27s IoT Village and DEF CON workshops. In his free time, he plays with RF toys, hikes to fire lookouts and catches everything at dodgeball.
Raised on a steady diet of video game modding, when Nathan found programming as a teenager, he fit right into it. Legend says he still keeps his coffee (and tear) stained 1980s edition of The C Programming Language by K&R stored in a box somewhere. A few borrowed Kevin Mitnick books later, he had a new interest, and began spending more and more time searching for buffer overflows and SQL injections. Many coffee fueled sleepless nights later, he had earned OSCP, and graduated highschool a few months later. After a few more years of working towards a math degree and trying fervently to teach himself cryptanalysis, he decided to head back to the types of fun hacking problems that were his real first love, and has worked at Security Innovation ever since.