– , Hackfest - Track 1 Language: English
This is an introduction to crypto: building blocks, protocols and attacks on them. We cover: encoding vs encryption, hashes, ‘classic’ crypto, stream ciphers, block ciphers, symmetric crypto, asymmetric crypto, has attacks, classic crypto attacks, stream cipher attack, block cipher attack models, ECB attacks, crypto protocols, digital signatures, message authentication code, nonces, simple authentication, challenge response, simple authentication attacks (key collisions, key extraction and extension, replay, valet, bad counter resync), MAC attacks, digital signature attacks, pubkey substitution, challenge response attacks (middleperson attack, UDS style seed-key predictions), WPA2 password cracking, WPA2 key reinstallation, WPA2 key nulling, TLS/SSL middleperson attacks, SWEET32, DROWN, logjam, POODLE, UDS seed-key exchange attacks (reverse key algorithm, lift key algorithm, solve for unknowns, retry-retry-retry, brute force, glitch past).
Tools covered include: rumkin.com, hashcat, john the ripper, binwalk, radare2, binvis.io, Veles, airocrack-ng, mitmproxy, MITMf.
The workshop is a ‘101’ level: geared for people good at computers but maybe no knowledge of cryptography. There will be minimal math (I promise). We’ll talk mostly about how to break bad crypto and bad crypto algorithms with 10-15min hands-on sessions integrated into 4 hours of workshop: Decrypt ‘Crypto’, Break Hashes, Break Crypto, Visualize Crypto.
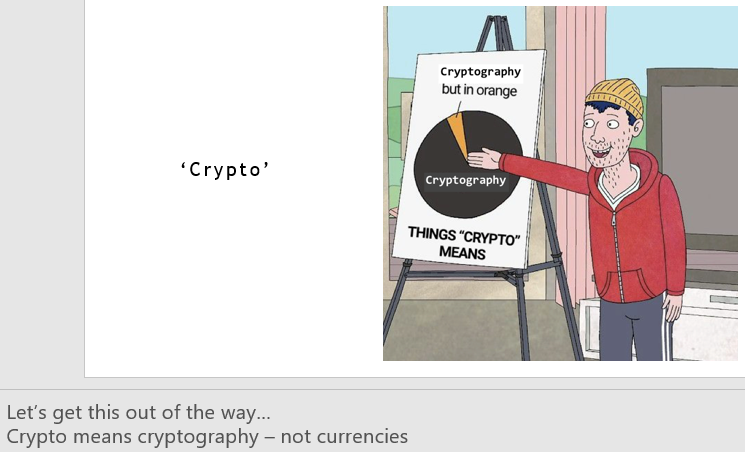
We will explore three applications of the building blocks and attacks also. Towards the end we tie-in the building blocks and attacks into how the following crypto protocols get broken: WPA2, TLS and UDS Seed-Key exchange (from automotive). Please join us for an intro-level exploration of cryptography building blocks, protocols and how to attack them. And, as always, crypto means cryptography.
Slides are available here https://drive.google.com/file/d/1xiY2B00GimSaXuFPR-1U9EKV2Vlf44GW/view?usp=sharing
Mr. Gardiner is a Cybersecurity Research Engineer at Yellow Flag Security, Inc. specializing in hardware and low-level software security. With more than ten years of professional experience in embedded systems design and a lifetime of hacking experience, Gardiner has a deep knowledge of the low-level functions of operating systems and the hardware with which they interface. Prior to joining the YFS team in 2019, Mr. Gardiner held security assurance and reversing roles at a global corporation, as well as worked in embedded software and systems engineering roles at several organizations. He holds a Masters of Engineering in Applied Math & Stats from Queen’s University. He is a DEF CON Hardware Hacking Village (DC HHV) and Car Hacking Village (CHV) volunteer. He is GIAC GPEN certified and a GIAC advisory board member, he is also chair of the SAE TEVEES18A1 Cybersecurity Assurance Testing TF (drafting J3061-2), and a voting member of the SAE Vehicle Electronic Systems Security Committee. Mr. Gardiner has delivered workshops and presentations at several world cybersecurity events including GENIVI security sessions, Hack in Paris, HackFest and DEF CON.